Read-Only by Default: Building Safer Production Database Workflows Without Slowing Engineers Down

Production databases sit close to real users, real money, and real incidents. Yet most teams still treat them like a general-purpose sandbox: open a GUI or CLI, point it at prod, and hand people a blank SQL canvas with broad write access.
“Just be careful” is the only real policy.
That works—until it doesn’t. A missing WHERE clause, a rushed hotfix, or a copy‑pasted query from staging can turn into:
- Silent data corruption
- Customer‑visible outages
- Incident calls that last hours instead of minutes
The usual reaction is to clamp down: more approvals, more tickets, more process. Engineers feel slower. Shadow tools appear. Risk doesn’t go away; it just moves.
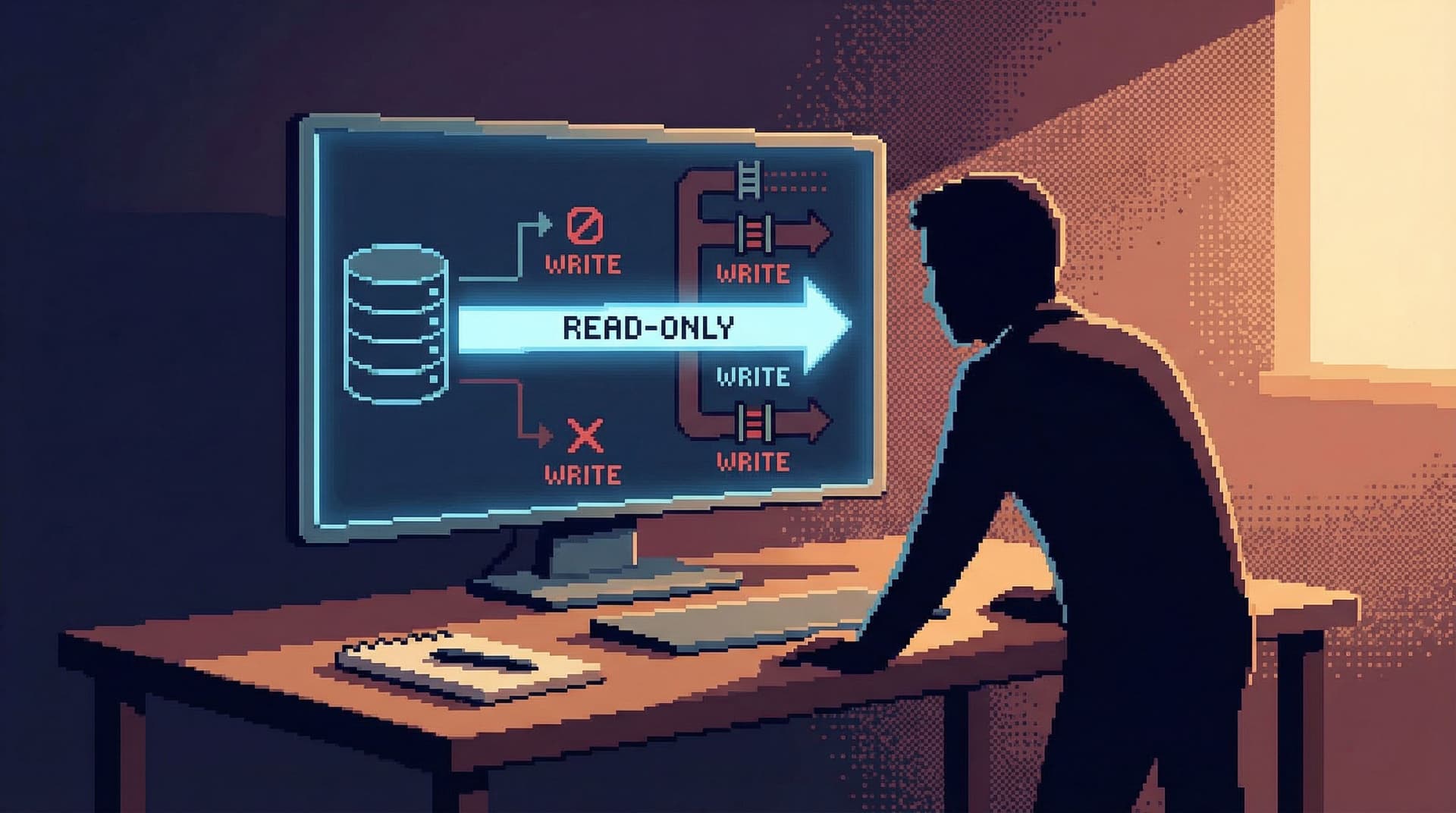
There’s a quieter, saner alternative: make read-only the default.
This post is about how to design read‑only‑by‑default production workflows that actually speed engineers up—by removing ambient risk, reducing noise, and making the safe thing the easy thing.
Along the way, we’ll draw on patterns that tools like Simpl are built around: opinionated read paths, calm defaults, and workflows that favor understanding over raw power.
Why Read-Only by Default Matters
Read-only defaults are not about distrust. They’re about shaping the first draft of how people interact with production.
A few reasons this stance pays off quickly:
1. Fewer incidents from “harmless” queries
Most high‑impact mistakes in production databases are not elaborate exploits. They’re small, plausible actions:
- A quick
UPDATEto “fix” a user row during an incident - A backfill run directly against prod instead of a job system
- A migration script pointed at the wrong database
In many incident postmortems, teams find that the person involved could have done the same investigation with read access only. The write was a shortcut, not a necessity.
When read-only is the default, those shortcuts require conscious friction: a different tool, a different role, a different environment. That alone prevents a surprising number of accidents.
2. Calmer engineers, faster investigations
When you know you can’t accidentally mutate prod from your primary tool, your brain relaxes. You:
- Explore more freely
- Try more hypotheses
- Share queries without worrying someone will reuse them dangerously
This is the same argument we made in “Safe by Default: Practical Patterns for Exploring Production Data Without Fear”: safety unlocks speed. Guardrails are not a tax; they are an enabler.
3. Cleaner separation between investigation and change
Read-only defaults force a simple discipline:
- Investigate in one place (read-only tools, logs, dashboards)
- Change in another (migrations, jobs, controlled scripts)
That separation aligns with how you already treat application code. You don’t hot‑patch production binaries in your debugger; you ship changes through a pipeline. Your data deserves the same respect.
What Read-Only by Default Actually Looks Like
“Read-only by default” is more than flipping a permission bit. It’s a set of choices about tools, roles, and workflows.
A practical setup usually includes:
- A primary production browser that is read-only for almost everyone.
- A small, audited path for writes to production data.
- Clear, opinionated read paths that make common investigations trivial without needing ad‑hoc writes.
Tools like Simpl lean into this: the default stance is “observe first,” with opinionated views and queries that encourage a read‑first workflow. If you haven’t seen it, “The Case for a Read-First Database Workflow” goes deeper on why that ordering matters.
Let’s break down how to put this into practice.
Step 1: Decide What “Read-Only” Means for Your Team
Not all read access is equal. Before you change tools or permissions, get specific about what “read-only” should cover.
At minimum, read-only in production usually means:
- No
INSERT,UPDATE, orDELETEfrom ad‑hoc tools - No schema changes (DDL) from general-purpose clients
- No long‑running or unbounded queries that can starve the database
A more mature stance also includes:
- Row‑level and column‑level restrictions for sensitive data (PII, secrets)
- Query timeouts and result limits to protect performance
- Safe defaults for isolation levels where your database supports it
Treat this like an API contract: what can a “normal” engineer do to production data from their day‑to‑day tools? Write it down. Make it boring.
Step 2: Make the Read-Only Path the Nicest One
If the read-only path feels cramped and the write‑capable path feels powerful, people will naturally gravitate toward the latter.
Flip that.
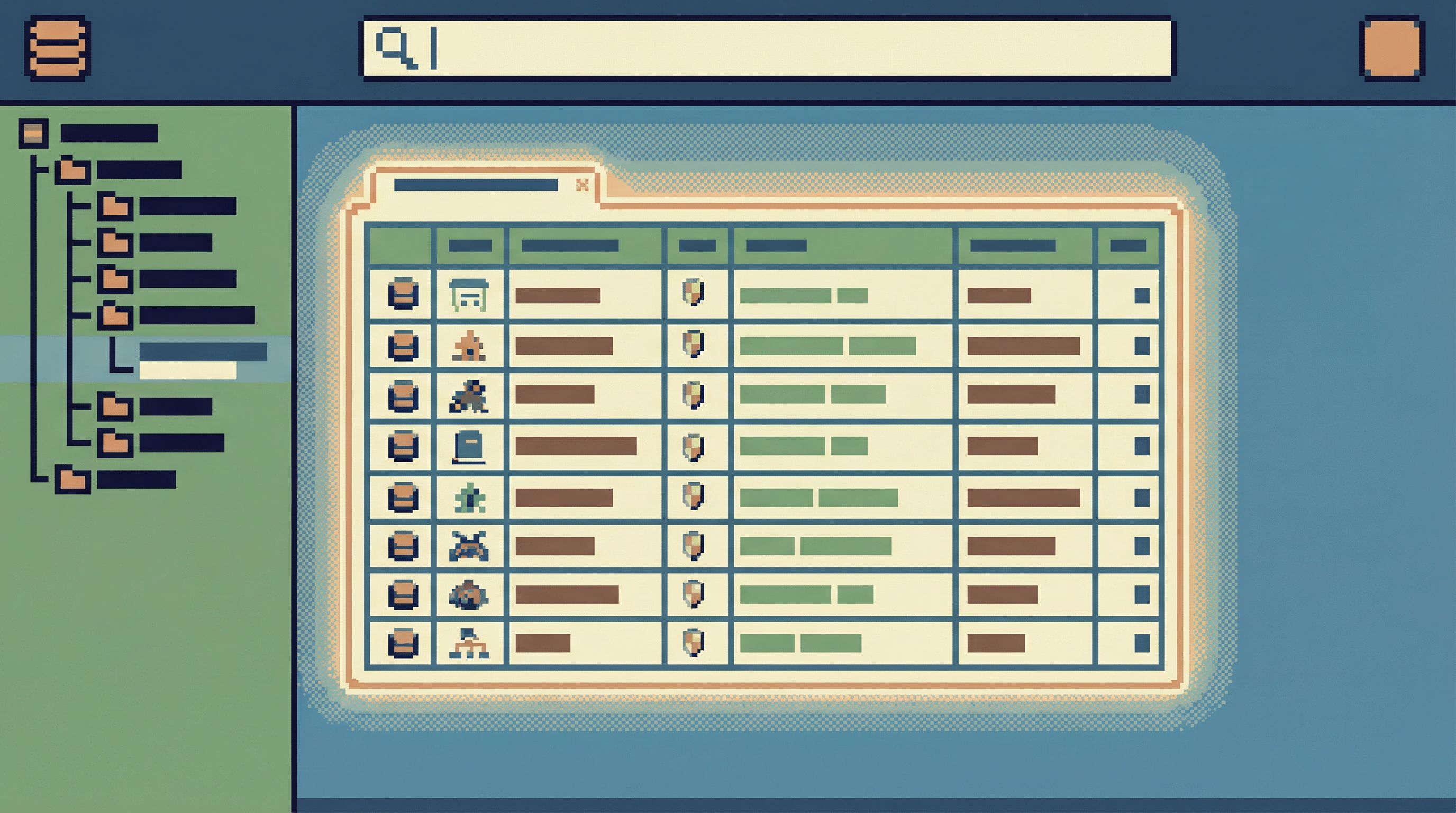
Design your primary production experience so that read-only is the most pleasant, capable way to answer questions.
Concretely:
- Use a focused browser instead of a full IDE. A tool like Simpl is built for calm exploration, not arbitrary mutation. Compare that to a heavyweight GUI that behaves like an IDE—something we unpacked in “Why Your Database GUI Feels Like an IDE (and Why That’s a Problem)”.
- Prebuild common views. Turn your recurring incident and support questions into opinionated read paths:
- “User profile + recent events”
- “Job run history + failure context”
- “Subscription state across billing + product tables”
- Favor trails over tabs. Instead of endless ad‑hoc queries, design flows that feel like a narrative: start here, then pivot there, then compare with this. “From Tabs to Trails: Turning Ad-Hoc Database Exploration into Reproducible Storylines” covers this pattern in detail.
When the read-only experience is fast, focused, and expressive, the desire to reach for write access drops sharply.
Step 3: Narrow, Audited Paths for Writes
You still need to change production data. The goal is not zero writes; it’s no casual writes.
Set up one or two clearly defined ways to mutate production data, and make everything else read-only.
Common patterns:
1. Migration and job systems only
- All structural changes (migrations) run through your deploy pipeline.
- All bulk data changes run as background jobs or one‑off tasks in the same system that runs your normal work.
- No ad‑hoc bulk updates from GUIs or CLIs.
This keeps risky operations in places that already have:
- Code review
- Rollback strategies
- Observability
2. Elevated roles with time‑boxed access
For the rare case where someone must edit a specific row in production:
- Use separate roles for read vs. write.
- Make write roles time‑boxed (e.g., temporary elevation for 30–60 minutes).
- Require a ticket or incident link for context.
- Log and review all manual writes.
The key is that write access is:
- Rare – not your hourly workflow
- Intentional – requires a few extra steps
- Traceable – easy to audit later
3. Safe, constrained admin surfaces
If you build or adopt internal tools for operations (refunds, account merges, manual corrections):
- Make them task‑specific, not general SQL canvases.
- Bake in domain rules (e.g., can’t refund more than X, can’t change status without reason).
- Keep them separate from your primary read-only browser.
The more you encode common write operations into narrow tools, the less anyone needs broad write access.
Step 4: Design Guardrails That Don’t Feel Like Handcuffs
Guardrails only work if people choose to stay inside them. If your policies feel punitive or slow, engineers will route around them.
Good guardrails share a few traits:
1. The safe thing is the default
- Opening your main database tool connects to read-only roles by default.
- The default views are SELECT‑only and scoped to the most common questions.
- Anything that looks like a write requires explicit opt‑in (different tool, different role, or both).
This is exactly the stance behind “Designing Calm Defaults: How Simpl Encourages Safer, Clearer Queries”: defaults are behavior.
2. Friction is proportional to risk
- Looking up a user’s recent events should be one click.
- Running a bulk correction script should require review, logging, and maybe a feature flag.
People accept friction when it’s clearly tied to impact. Make that mapping obvious.
3. Feedback is immediate and clear
When someone hits a guardrail—say, they try to run an UPDATE in a read-only context—your tools should:
- Fail fast, with a clear explanation
- Suggest the correct path (“Use the incident correction flow” or “Open the operations tool”)
- Avoid cryptic database errors that feel like bugs
A calm, opinionated browser like Simpl can embody this: you don’t just get a generic permission error; you get a nudge toward the workflow your team actually wants.
Step 5: Align Incident Workflows with Read-Only Defaults
Incidents are where your policies get stress‑tested. Under pressure, people revert to whatever is fastest.
To keep read-only as the default even during outages:
-
Make your incident runbooks read-first.
- Step 1: inspect key tables and events in a read-only browser
- Step 2: validate hypotheses with additional queries
- Step 3: only then consider targeted writes or config changes
-
Prebuild incident views.
- “Recent errors by service and user”
- “Recent deploys and related schema changes”
- “Hot partitions / tables by query volume”
You don’t want to be inventing these queries while the pager is going off. Posts like “Incident Triage Without the Firehose: A Focused Approach to Production Data During Outages” and “The Minimalist’s Guide to Database Debugging in Incident Response” go deeper on this style.
-
Separate incident write tools.
- If you must run emergency corrections, do it from a dedicated incident tool or script path.
- Log everything with incident IDs.
- Review these writes in the postmortem.
The goal is simple: during an incident, nobody should be asking “Is it safe to open the database?” It should already be safe—because their default tools cannot break prod.
Step 6: Reduce Context Switching Around Production Data
One quiet way read-only defaults speed engineers up: they enable simpler, more integrated workflows.
When you’re not worried about accidental writes, you can:
- Embed production views directly into debugging tools
- Link from dashboards straight into row‑level context
- Let support and product teams self‑serve more of their own questions
This reduces the “side quests” of database work—bouncing between SQL clients, dashboards, logs, and Slack. If that pattern is familiar, “Database Work Without the Side Quests: Reducing Context Switching in Day-to-Day Queries” is worth a read.
Read-only by default is what makes this safe. You can expose more of the database to more people because the worst they can do is misunderstand, not mutate.
Step 7: Socialize the New Defaults
The technical changes are the easy part. The hard part is shifting habits.
A few ways to make read-only by default stick:
- Announce the change as a benefit, not a restriction. Emphasize fewer incidents, calmer incident response, and safer exploration.
- Update onboarding. New engineers should learn the read‑only browser first, and only later hear about the narrow write paths.
- Capture “wins.” When a near‑miss or prevented incident happens because someone couldn’t run a risky query, share that story.
- Keep the write path honest. If you find people frequently requesting write access for the same task, that’s a signal to build a safer, narrower tool or read path.
Over time, “I’ll just check in the read‑only browser” becomes the default sentence. That’s when you know the culture has shifted.
Bringing It All Together
Read-only by default is not about slowing engineers down. It’s about:
- Removing ambient risk so people can think clearly
- Separating investigation from change
- Making focused, read‑first workflows the path of least resistance
A practical implementation looks like:
- Clear definition of read-only capabilities in production.
- A primary, pleasant read-only browser—ideally opinionated and calm, like Simpl.
- Narrow, audited paths for writes through migrations, jobs, or constrained tools.
- Guardrails that scale with risk and provide clear feedback.
- Incident workflows that stay read-first even under pressure.
- Reduced context switching by safely exposing more read access to more people.
- Cultural reinforcement through onboarding, stories, and continuous refinement.
When you design your tools and habits around these principles, production stops feeling like a minefield. It becomes what it should have been all along: a clear, trustworthy source of truth you can interrogate without fear.
Take the First Step
You don’t need a full permissions overhaul to start.
This week, you can:
- Pick one production database tool and switch its default role to read-only.
- Identify the three most common production questions your team asks, and turn them into saved, read‑only views.
- Write down your current write paths to production data and circle the ones that feel too casual.
From there, iterate. Tighten one guardrail. Add one opinionated read path. Retire one risky habit.
If you want a tool that’s built around these ideas from the ground up, take a look at Simpl—an opinionated database browser designed to make read‑first, safe‑by‑default production work feel calm instead of brittle.
Read-only by default is not a feature. It’s a posture. Once your team adopts it, the work around your databases gets quieter, safer, and—paradoxically—faster.