The Calm Access Model: Structuring Roles Around Real Read Work, Not Org Charts

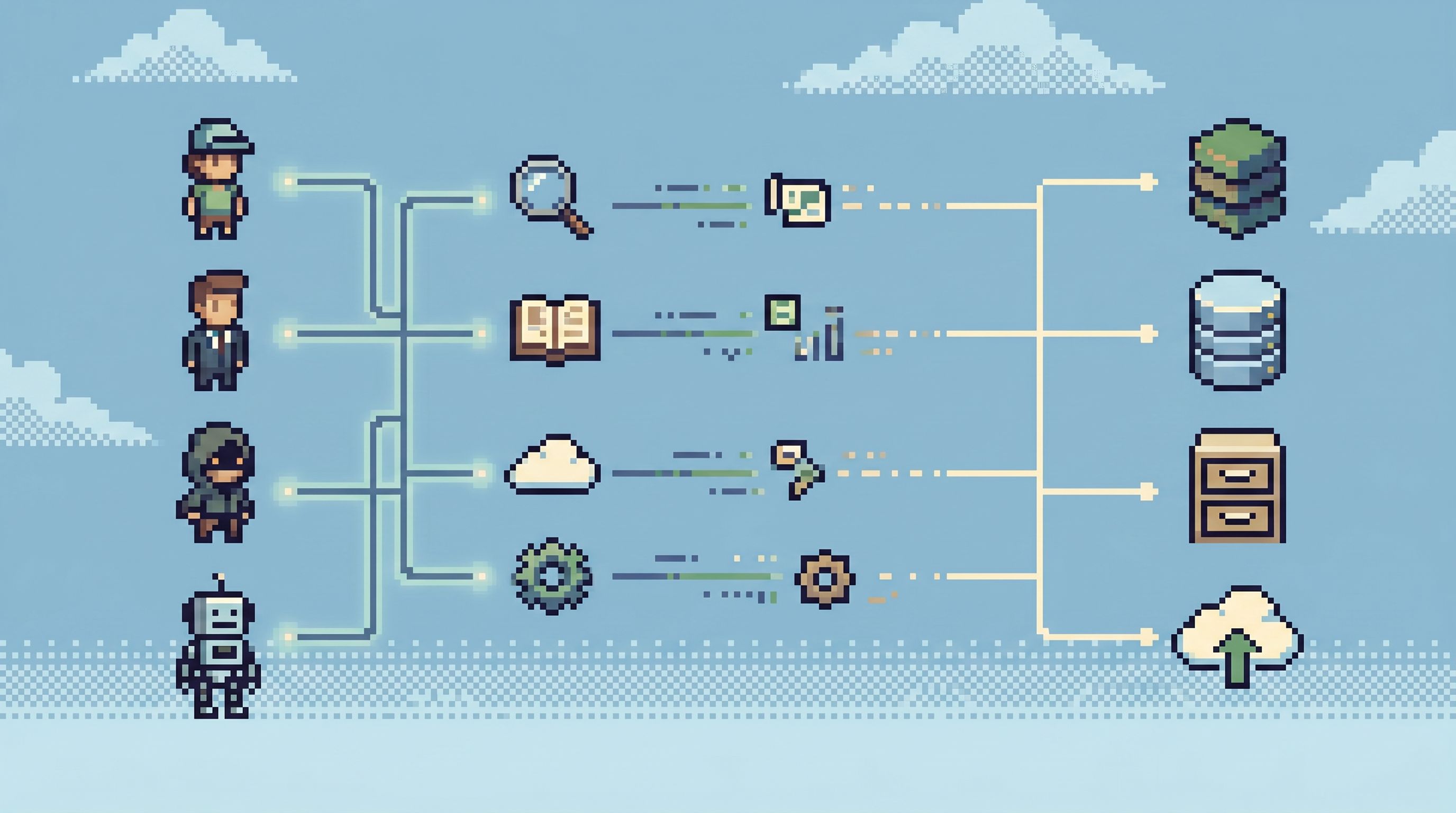
Most teams design database access the same way they design seating charts:
- Start from the org chart.
- Map titles to roles.
- Hand each role a bundle of permissions that feels “about right”.
It looks reasonable. It ships quickly. And a year later, you have:
- Over‑privileged engineers who can see and do far more than they ever use.
- Support and product teams blocked on “someone with prod access”.
- A compliance story that only exists in a spreadsheet.
- Debug work that happens in DMs and screenshots instead of calm, repeatable paths.
There’s a quieter alternative: design access around real read work — the concrete questions people actually ask of your databases — instead of around your reporting lines.
This is the Calm Access Model.
It’s not a new standard or a framework. It’s a stance:
Start from the reads you want to be easy, safe, and repeatable. Then let roles fall out of that.
Tools like Simpl are built around this stance: an opinionated database browser that treats read flows as first‑class, and lets you encode access in terms of those flows instead of a giant permission matrix.
Why org‑chart access quietly fails
Org‑chart access control feels natural because it mirrors how companies think about responsibility. But databases don’t care about reporting lines. They care about questions.
Common symptoms when you design access from titles instead of tasks:
- Role sprawl – every reorg or new title adds a new role. No one wants to delete old ones. You end up with dozens of slightly different “Engineer”, “Senior Engineer”, “Staff Engineer” roles.
- Permission creep – exceptions accumulate. One ticket gets solved by “temporarily” adding
SELECTon a sensitive table to a broad role. The temp change becomes the new default. - Shadow access – when the official path is slow or unclear, people share credentials, run queries from screenshots, or ask “someone who has prod” to paste results into Slack.
- Debugging by heroics – incidents depend on whoever remembers the right query and still has the right access.
Security teams see the same pattern from a different angle: over‑privileged accounts are now a leading factor in identity‑based attacks and breaches, especially when third‑party or machine identities are involved. Over‑permissioned roles become the blast radius when something goes wrong.
The problem isn’t just security. It’s attention.
When access is broad and unstructured, every database session is a blank canvas. You’re not guided to the small set of reads that matter for your work. You’re staring at a schema forest.
We’ve written before about the cost of this in incident workflows in Post-Dashboard Debugging: Why Incident Workflows Need Trails, Not Tiles. The same idea applies to access: you want trails, not tiles of permissions.
A calmer premise: roles follow read paths
The Calm Access Model starts from a different question:
“What are the recurring reads we want this person to be able to do, safely, with low friction?”
Not:
- “What’s their level?”
- “Which team are they on?”
- “What does our HR system call this role?”
If you list out the actual reads your team runs in production, patterns appear:
- “Look up a customer by ID and see their last N orders.”
- “Inspect a failed payout and its retries.”
- “Verify that a migration touched the expected tenants and nothing else.”
- “Check a feature flag’s rollout for a specific cohort.”
These are flows, not tables.
A calm access model says:
- Make those flows first‑class and repeatable.
- Bind access to those flows.
- Only then, group flows into roles.
Simpl leans into this: you define opinionated read paths (templates, trails, “runbooks in SQL”), and then decide who can run which paths, instead of who can SELECT from which raw tables.
Principles of a Calm Access Model
You don’t need new infrastructure to adopt this stance. You need a few strong opinions:
-
Read‑first, write‑rare
- Make read access the default surface for most people.
- Keep writes (schema changes, data fixes) in narrower, audited tools.
- A focused, read‑only browser like Simpl sits neatly between admin consoles and CLIs.
-
Flows over objects
- People think in stories: “this user’s refund”, not “joins across
users,orders,payments,refunds”. - Access should be framed around those stories: pre‑scoped queries, filtered views, guided navigation.
- People think in stories: “this user’s refund”, not “joins across
-
Least privilege, but human
- The principle of least privilege is simple in theory; in practice, the hardest part is cleaning up the access you’ve already granted and making the safe path the easy path.
- Calm access doesn’t mean nobody can see anything. It means:
- Every permission has a clear reason.
- Every permission is attached to a named flow.
-
One primary entry point
- If you have five ways into prod data, you don’t have an access model; you have a maze.
- Aim for one calm entry point for read work (a browser like Simpl), with other tools reserved for specialist tasks.
- We explored this idea deeply in The Calm Query Session: Designing Database Work Around One Entry Point, Not Ten.
Step 1: Inventory real read work
Before you touch roles, you need to understand what people actually do.
Spend one or two weeks observing:
- Incident channels.
- Support escalations.
- Common “Can someone check prod?” requests.
- Ad‑hoc queries in shared docs or BI tools.
Capture concrete reads, not abstractions:
- “Support looks up users by email to confirm subscription status.”
- “On-call checks a job’s last 20 executions across three tables.”
- “Data engineers validate backfills by sampling affected tenants.”
Write them in a simple template:
- Who: which persona runs this read?
- Trigger: what event starts it? (ticket, alert, weekly report)
- Scope: which entities? (user, order, tenant, job)
- Tables / views: what data does it touch today?
- Risk level: is this sensitive? regulated? internal‑only?
You’ll probably find that 60–80% of your real read work clusters into a small set of patterns. That’s what you want.
Step 2: Turn recurring reads into calm paths
Once you see the patterns, the next step is to encode them.
Instead of:
- “We have a doc with useful SQL.”
Aim for:
- “We have a handful of named, opinionated paths that anyone in this role can run safely.”
Concretely, for each recurring read:
-
Write the query you wish people ran
- Proper filters.
- Clear ordering.
- Safe limits.
- Masked or redacted sensitive fields where possible.
-
Wrap it as a first‑class object
- In Simpl, this looks like a quiet query template: parameterized, named, and saved as part of a trail.
- We go deeper on this pattern in The Quiet Query Template: Turning Recurring Debug Flows into Opinionated, One-Click Reads.
-
Define parameters, not free‑form SQL
- Let people plug in
user_id,order_id, or a date range. - Don’t let every support request become
SELECT * FROM users LIMIT 1000.
- Let people plug in
-
Document the intent
- Short description: “Use this to investigate a stuck payout from the support queue.”
- Link to the playbook or runbook if it exists.
The goal is that a new teammate can:
- Open your database browser.
- Choose “Investigate failed payout”.
- Fill in an ID.
- Land on a calm, scoped view of exactly what they need.
Not:
- Open a SQL IDE.
- Paste a query from Slack.
- Hope their role has the right permissions.
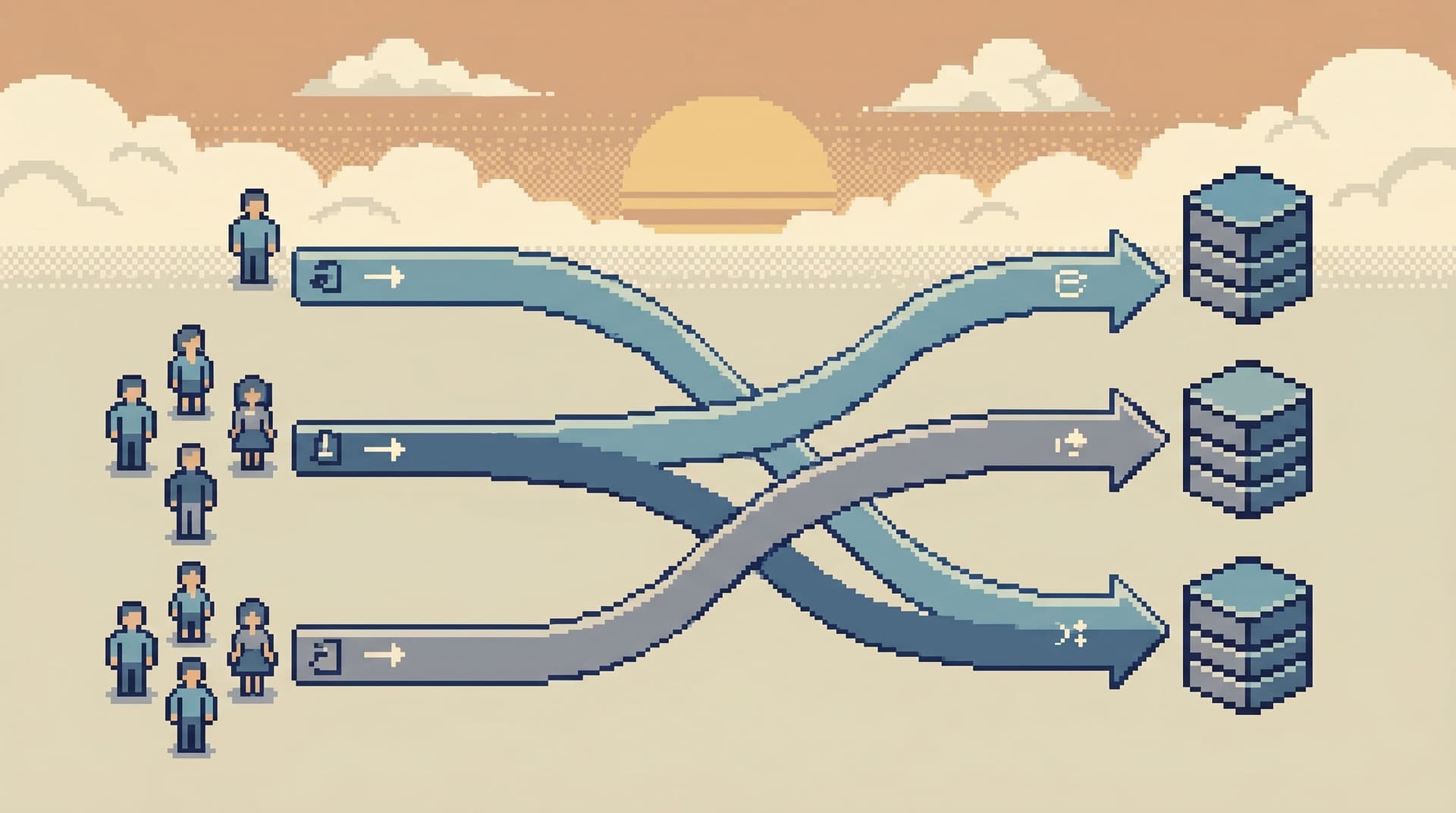
Step 3: Build roles from paths, not titles
Now you’re ready to talk about roles — but they’re not HR roles. They’re access bundles of paths.
For example:
1. Support Reader
- Can run:
- “Lookup user by email.”
- “Inspect latest orders and payments for a user.”
- “View subscription and billing status.”
- Constraints:
- PII masked where not needed.
- Only reads; no writes.
- Hard limits on row counts and time windows.
2. Incident Reader
- Can run everything Support Reader can, plus:
- “Trace a request across services.”
- “Inspect failed jobs for a tenant.”
- “Check recent schema changes affecting this table.”
- Constraints:
- Broader visibility, but still read‑only.
- Queries are pre‑scoped to incident‑relevant entities.
3. Data Engineer / SRE
- Can run all incident paths, plus:
- “Sample backfilled rows.”
- “Validate migration for tenant cohort.”
- A small number of exploratory views on key tables.
Each role is now:
- A named set of paths.
- With clear intent.
- And auditable scope.
The org chart still matters, but only at the edge:
- HR titles → mapped to one or more path‑bundled roles.
- Contractors or vendors → mapped to the minimum set of paths they truly need.
Step 4: Tighten raw access behind the browser
Once you have flows and path‑based roles, raw access becomes the exception, not the norm.
A calm pattern looks like this:
- Primary interface: a focused browser like Simpl for 90% of read work.
- Raw SQL: limited to a smaller group, used for:
- Schema design.
- Complex migrations.
- Rare investigations that don’t fit existing paths.
- BI / dashboards: used for trends and monitoring, not for per‑user or per‑incident reads.
This has a few benefits:
- Smaller blast radius – if a support account is compromised, the attacker only gets the scoped paths, not arbitrary
SELECTon every table. - Cleaner audit trails – instead of a wall of random queries, you see “Support Reader ran ‘Lookup user by email’ with parameters X”.
- Easier onboarding – new teammates learn a small set of paths, not an entire schema.
We’ve described this middle layer in detail in Read-Only, Opinionated, and Enough: A Minimalist Stack for Everyday Production Data Work.
Step 5: Clean up legacy roles without breaking work
The hardest part is not designing the new model. It’s migrating to it without stalling the team.
A calm migration plan:
-
Shadow the old model
- Keep existing roles.
- Introduce the new browser and path‑based roles in parallel.
- Encourage new work to start from paths, not raw queries.
-
Log and compare
- Track which old permissions are actually used.
- Map those uses back to your new paths.
- If someone runs a one‑off query more than a few times, consider adding a new path.
-
Narrow in layers
- First, remove obviously unused roles.
- Then, narrow broad roles by moving people to path‑bundled roles and keeping a small “escape hatch” for rare cases (with review).
-
Make escalation explicit
- If someone needs more access:
- They request a specific path, not “prod access”.
- You review the risk and either:
- Add them to a role that includes that path, or
- Add a new, better‑scoped path.
- If someone needs more access:
-
Narrate the change
- Explain that this is not about locking things down for the sake of it.
- It’s about:
- Faster, calmer incident work.
- Clearer expectations.
- Less time hunting for “the right query”.
Step 6: Treat access as part of your read design
In a calm model, access is not a separate compliance project. It’s part of how you design read flows.
When you create a new trail or template:
- Ask: Who should be able to run this without supervision?
- Decide:
- Which role(s) get it by default.
- Whether the output should be masked or aggregated.
- Whether it belongs in staging only, or both staging and prod.
This is where tools like Simpl shine: the unit of access is not just “table” or “database”. It’s a named, opinionated path.
Over time, you end up with:
- A small catalog of trusted paths.
- A clear mapping from personas → roles → paths.
- Less pressure to hand out blanket prod access “just in case”.
What this feels like day to day
When you get the Calm Access Model right, daily work changes in subtle ways:
- Support doesn’t paste screenshots of admin consoles into Slack; they paste links to trails.
- On‑call engineers don’t ask “who has prod?”; they open a known incident path and start reading.
- New hires don’t need a schema tour before they can help; they start from curated reads.
- Security reviews talk about “who can run this path” instead of “who has SELECT on this table”.
Incidents feel less like a scramble across ten tools and more like following a story, as we explored in Less Tabs, More Trails: Structuring Long Debugging Sessions as One Continuous Read Path.
Where to start this week
You don’t need a full redesign to get value. A minimal first step:
-
Pick one high‑leverage persona
- Often: support, on‑call, or product engineers.
-
List their top 5 recurring reads
- Real examples from the last month.
-
Turn 2–3 of those into named paths
- Use your existing tools, or try a browser like Simpl to encode them as templates.
-
Give that persona a single, path‑based role
- Start small and explicit.
-
Route the next incident or ticket through that path
- Notice what got easier.
- Notice what still required raw access.
Repeat. Each new path you encode is one less reason to hand out broad permissions.
Summary
- Org‑chart‑driven access leads to role sprawl, permission creep, and noisy, fragile workflows.
- A Calm Access Model starts from real read work: the concrete questions people ask of your data.
- You:
- Inventory recurring reads.
- Turn them into calm, opinionated paths.
- Build roles as bundles of those paths.
- Tighten raw access behind a focused browser like Simpl.
- Treat access decisions as part of designing read flows, not an afterthought.
- The result is:
- Safer production data work.
- Faster, calmer incidents.
- Clearer onboarding and expectations.
Take the first step
Don’t start with a new RBAC matrix. Start with one question:
“What are the five reads we wish everyone on this team could run safely, without asking for help?”
Write them down.
Turn one of them into a named, reusable path — in your current stack, or in a focused browser like Simpl.
Then give a real person access to that path, not to a bucket of tables.
That’s the Calm Access Model in miniature: roles that follow the work, instead of the org chart. From there, you can grow it one quiet read at a time.